These days it's strange to hear people say, "I'm just not computer literate," as computers have evolved from archaic scientific calculators to simple point-and-click type machines. We suspect that today's "computer illiterates" are people who haven't taken the time to experiment with such a machine. And we strongly believe that spending just twenty minutes with one could turn the most adamant technological caveman into any one of those who have fun wreaking chatroom havoc on the Internet today.
Today, one only needs to learn how to manipulate a mouse, punch a few buttons on a keyboard, or really just turn the thing on to use a computer. It's hard for some folks to believe, but the computers of this generation almost run themselves! For fun, let's investigate just how little knowledge these thousand-dollar machines actually require.
Can an absolute newbie operate a computer without knowing how to use a mouse or keyboard? Assuming that a computer is set up to operate on voice command - sure! Voice command software allows users to tell a computer what to do and the computer responds by fulfilling the user's commands. Although it's pretty new and still under development, voice directed technology has already infiltrated consumer service related systems.
Think back to the last time that you paid a bill over the phone. Instead of speaking to a human being, chances are that you spoke to a computer that not only responded to what you said and followed the commands that you gave it, it also asked you for more information such as your full name or credit card number. In this case, a person (such as yourself) operated a computer without even knowing it!
Can an absolute newbie sit down at a computer without knowing how to use one? Assuming that a computer is set up to operate on touch command - the answer is again, yes! Touch command software allows users to literally touch objects on a monitor and tell the computer what to do with a finger. Known as "kiosks," these programs are already in use world wide at ATM machines, employment centers, and in health monitoring systems.
Neither a mouse nor a keyboard is required. A computer user only needs to touch various boxes on a screen to control a computer. Sure, the programming behind such technology is extensive and advanced, but to the end user, it makes computer use less intimidating and plain easy.
Of course when we talk about operating a computer, we envision more involvement than speaking on the phone or touching things on a screen. The above illustrations were just a couple of examples of how far computer technology has grown, and how far we've pushed "user-friendliness" to its limit. Eventually, the keyboard and mouse will have to play a role when computer newbies have to work with one as a cash register, as a hotel booking program, or as a library's catalog system.
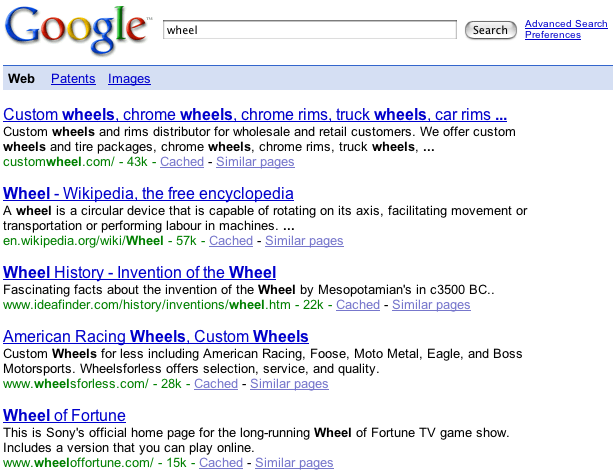
These requirements don't make computers any less easier to operate, but they don't make them that much harder either. So much of today's software is designed to accommodate the experience of a new user that anyone could get connected to the Internet, send an email message, and download an MP3 file within the first five hours of purchasing a personal PC.